Crypto 101
Hi a field of computer science to send and receive messages between a sender and receiver in the most secure way possible – Cryptography
Crpytogrpahy- the practice and study of hiding information.
Below are the various methods which have been deployed over centuries to for secure exchange of information.
Starting from one of the ancient techniques of creating a ciper text
Technique 1.0
CEASER CIPHER – employed by the famous Roman king Julius Ceaser
According to this technique person looks up each letter of the message in the “plain” line and writes down the corresponding letter in the “cipher” line. Deciphering is done in reverse, with a right shift of 3.
Plain: ABCDEFGHIJKLMNOPQRSTUVWXYZ Cipher: XYZABCDEFGHIJKLMNOPQRSTUVW
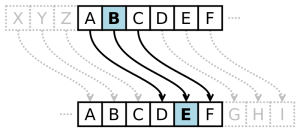
- Mathematical representation for encryption of plain text
- x={A=0 ,B=1,C=2,……Z=25}
- n=3

- Mathematical representation for decryption of cipher text

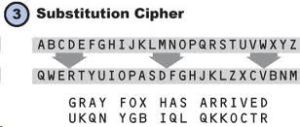
- Technique1.1
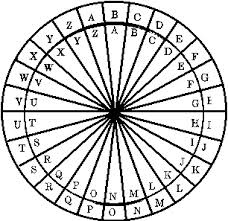
- Similar to Ceaser Cipher is a technique employed by present day experts is the SUSTITUTION CIPHER , the shifteing algorithm works just the same way besides the size of shift varies according to the sender
- ———————————————————————————————————————-
- Technique 2.0
- The next comes a different encryption technique the VERNAM Cipher ,as the name suggest it was invented and planted by Gilbert Vernam .


- ————————————————————————————————————————-
- Under this technique ,binary equivalent of each alphabet is taken which is Xclusively ORed (XOR) with a random stream of numbers ,and we take modulus value against 26 ,this value is converted to alphabets , and hence the cipher text is obtained.
- Technique 3.0